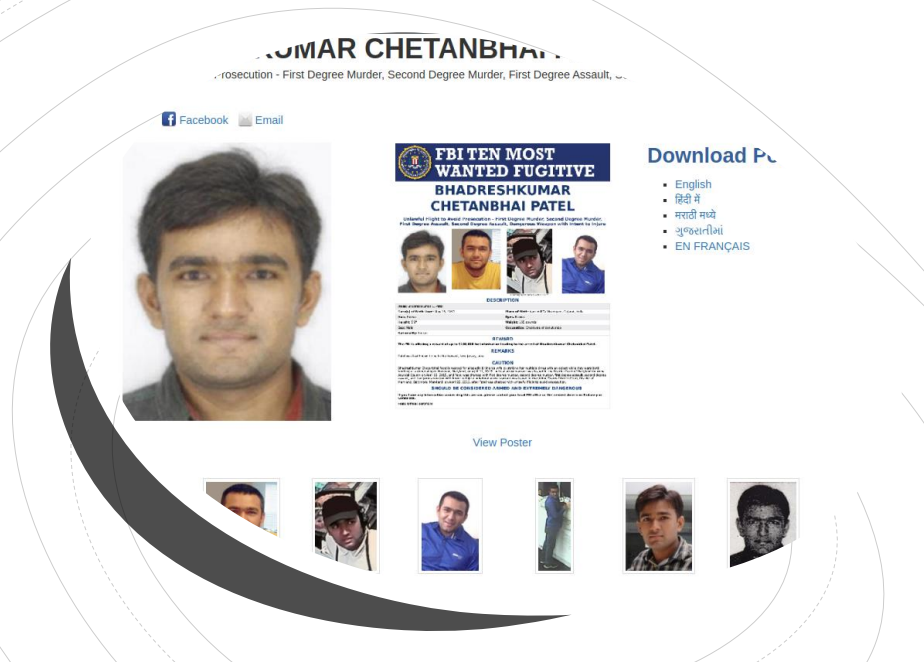
Curated Intelligence's cyber sleuth - BOsintBlanc - recently demonstrated how to use his OSINT workflow for finding people (see here) to locate some of the online presence of one of the FBI's Most Wanted as a proof-of-concept (PoC).
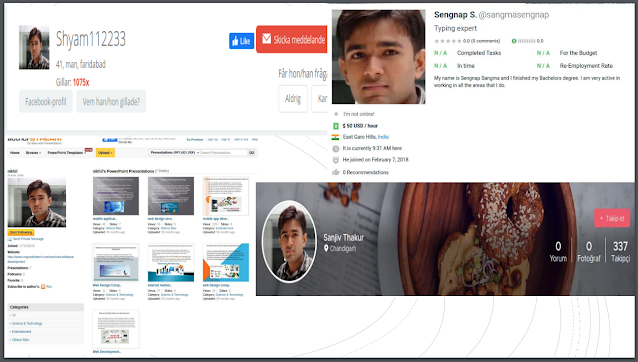
BOsintBlanc first searched the target's name and "Maryland" on Facebook, which returned a user profile with the same picture as the target. This was followed by using a reverse image search in Yandex, which uncovered a number of freelancer job adverts with new aliases - not listed on the FBI's notice. These aliases were then used to pivot and uncover additional artefacts connected to the target. This included checking breach data for usernames and email addresses, which could also be used to locate further details.
The full slide desk is available on BOsintBlanc's GitHub page here.
Curated Intel Community Features are sourced using our Member Content channel on Discord. If you have recently produced a noteworthy piece of writing, a project, a podcast, an infographic or other CTI content let us know!