Background
The Curated Intelligence community is a group of analysts from around the world that tracks the latest updates on the threat landscape. The latest situation Curated Intel has been following is the Hamas terrorist attack against Israel on 7 October 2023. The attack has subsequently resulted in thousands of civilian casualties on both sides and has destabilized the region.
As with any modern conflict, cyber activity surrounds it from all nature of groups. The most widely recognised and surface-level type has been hacktivism due to the public announcements by threat actors claiming responsibility for attacks. This often takes on social networking sites, like Telegram and Twitter, among others.
There has also been examples of the cybercrime underground exploiting the situation for financial gain. This includes offering databases of stolen data for sale as well as live access to compromised systems. This is typical behaviour for cybercriminals, but it should not be ignored by defenders in the region.
Regional advanced persistent threat (APT) groups are also expected to be launching campaigns following the incident. It should be noted that reporting on APT group activity often lags behind due to the typical covert nature of their operations, but various well-known groups are almost certainly going to be active during this tumultuous time.
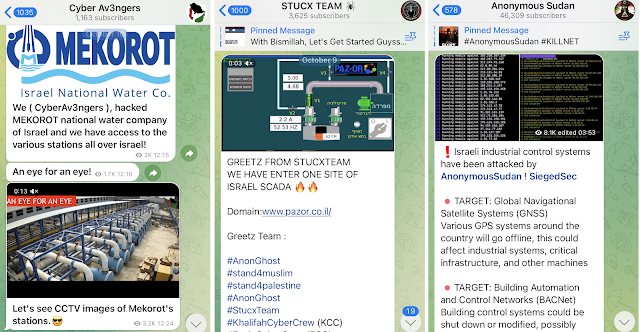
Hacktivism
The type of hacktivism surrounding this conflict often dominates the media headlines and social media circles because it is public and easy to find. It is difficult, however, to verify and debunk their claims. Therefore, spreading their claims can lead to propagating misinformation. Then, by the time hacktivist claims have been debunked, it is often too late as the lie is usually always more likely to be viewed than the fact check.
Examples on Telegram include threat actors screenshotting access or lists of IP addresses and claiming that they have hacked them. From these messages alone, it cannot be assumed that they were successful as time and time again, these threat actors have proven to be lying.
Ultimately, the goals of these hacktivists are merely to intimidate and cause issues for their targets. The secondary effect is that cybersecurity and intelligence teams have their resources consumed trying to verify if any of these claims are legit, when arguably most of the time these groups are making it up. Some researchers have begun to take the time, in one notable example, to debunk these groups that are known to regularly exaggerate their claims.
The most common types of successful hacktivist attacks have been observed during the war in Israel have been denial of service (DoS) attacks on websites and mobile applications, as well as website defacements. This is because of the low-skilled nature related to these attacks. They can, however, be proven by showing the site as offline and showing a site that has been defaced.
In some cases, however, the hacktivists have been able to execute disruptive attacks on Israeli civil services, such as the manipulation of the RedAlert app API, which is used in Israel to warn civilians about incoming Hamas or Hezbollah missile barrages. This incident also reportedly led to the app being removed from the Google Play Store and prohibited from launching.
Palestine has been attacked by pro-Israeli hacktivist groups as well. One key example thus far involves the Palestinian ISP Alfanet that was targeted by a destructive attack. An adversary known as ThreatSec reportedly breached Alfanet and shutdown its servers. Technical details about the incident have not yet been shared.
Various researchers have shared their resources related to tracking the Israel-Palestine conflict. This includes CyberKnow's CyberTracker, CrowdStrike's Pyramid of Adversaries, and FastFire's GitHub Resource of Telegram channels. We recommend using these resources to track adversary activities, which can be done live and on a daily basis. Cybercrime Underground
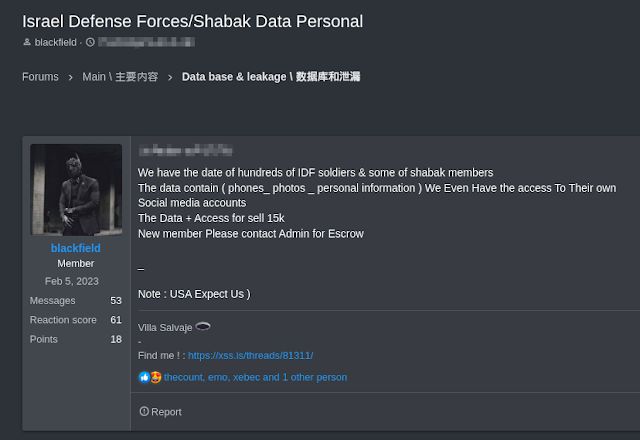
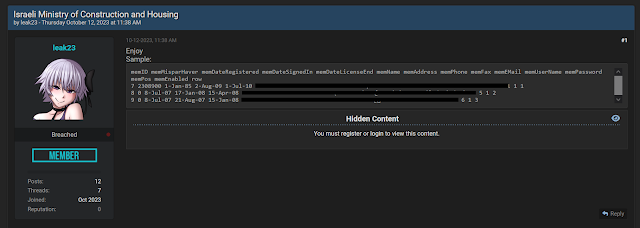
As with any major historical event or catastrophe, cybercriminals will seek to exploit the situation. It is to be expected now that there will always be fake websites scamming those trying to donate to causes, whether it is for Israel or Palestine.
Some cybercriminals from the English-speaking and Russian-speaking forums are attempting to profit off of the war by offering stolen databases from Israeli and Palestinian organizations. The stolen data could be weaponized for all sorts of attacks, including phishing, identity theft, and account takeovers, among types of attacks.
IDF/Shabak personal data was offered on RAMP (Russian-speaking forum)
Israeli MoCH data was offered on BreachForums2 (English-speaking forum)
Palestine Communications data was offered on BreachForums2 (English-speaking forum)
Defenders in the region should also not discount the fact that organized cybercrime groups running ransomware operations may also seek to exploit the situation and attack while resources are strained. One month before the war in Israel began, the RagnarLocker ransomware group attacked Israel's Mayanei Hayeshua hospital. During the time of war, such destructive attacks on hospitals are going to cause much more significant strain and impact on the targeted victims. APT Groups
At the time of writing, there has been a minimal amount of public reports related to APT group activity that's potentially related to the war in Israel. But that does not mean there are not many groups currently launching campaigns. Due to the nature of these APT groups, they are almost certainly going to seek to exploit the situation to conduct intelligence gathering operations.
Usefully, Secureworks publicly shared their database of threat actor profiles in the past and continue to keep it updated. This enables us to search for APT groups that target Israel and begin to predict which APT actors are potentially going to be launching attacks. Examples of APT actors that are likely to be involved in the conflict at some stage could include: - COBALT AZTEC, an Iranian state-sponsored threat group that operates and distributes DarkBit ransomware in destructive cyber attacks.
- COBALT FOXGLOVE, an Iranian threat group that exploits VPN and network appliance vulnerabilities to gain remote access to targets, usually dropping a web shell shortly after successful exploitation.
- COBALT LYCEUM, an Iranian state-sponsored threat group known for targeting critical infrastructure organizations, such as telecommunications, oil and gas companies as well as government entities.
- COBALT MIRAGE, an Iranian state-sponsored threat group known for delivering ransomware attacks using BitLocker and DiskCryptor to encrypt systems
- COBALT SAPLING, an Iranian threat group that uses the Moses Staff persona, styling themselves as a pro-Palestinian hacktivist group with a stated aim of harassing and disrupting businesses and government entities in Israel.
- COBALT SHADOW, an Iranian threat group that uses the BlackShadow persona, that has conducted multiple high-profile hack-and-leak attacks against companies in Israel, involving the distribution of personal information.
Other regional APT actors deemed worth tracking and investigating their TTPs by Curated Intel are also as follows:
- POLONIUM, a Lebanon-based and Hezbollah affiliated APT group that launches cyber-espionage campaigns against Israel and likely collaborates with Iranian intelligence services.
- Volatile Cedar, a Lebanon-based and Hezbollah affiliated APT group that launches cyber-espionage campaigns against Israel and elsewhere.
- Dark Caracal, a state-sponsored APT groups attributed to the Lebanese General Security Directorate that launches cyber-espionage campaigns against Israel and elsewhere.
- Molerats, a Gaza-based and Hamas affiliated APT group that launches cyber-espionage campaigns against Israel.
- AridViper, a Palestine-based APT group that launches cyber-espionage campaigns against Israel.
Conclusion
The Curated Intelligence community shall continue to track hacktivist, cybercriminal, and APT group activity surrounding the war in Israel. We are fortunate to have a strong network of industry and public sector connections that allow us to send information to where it needs to go. We pray for peace in the region.