By: @BushidoToken
Introduction
Virus Total (VT) is one of the most useful tools in an analyst's toolbox. For a number of reasons, it is often the first place an anaylst may visit. This includes checking to see if a file is malicious, investigating a domain or IP address, as well as looking for malware samples and other indicators of compromise (IOCs). Any researcher or analyst should be well acquainted with VT. Its most powerful component is that anyone, from anywhere in the world can submit files and other IOCs. This means that researchers can uncover attack campaigns happening globally in near real-time, as well as those from months or years ago.
This blog covers how to utilise Virus Total for investigations and triage. The first and one of the most important things to remember is that something is uploaded to VT it is publicly accessible and submitted to over 70 antivirus engines for analysis.
The devil is in the details 👿
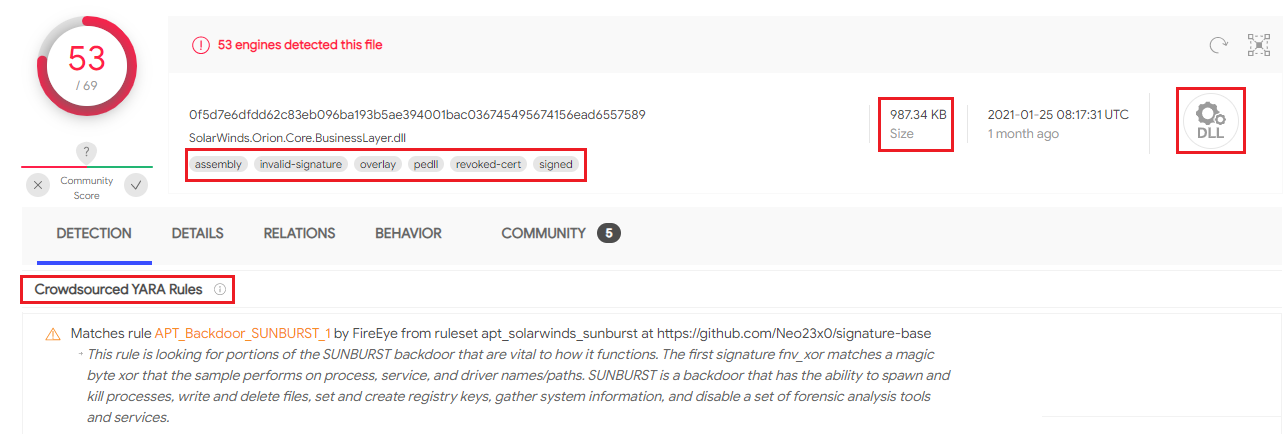
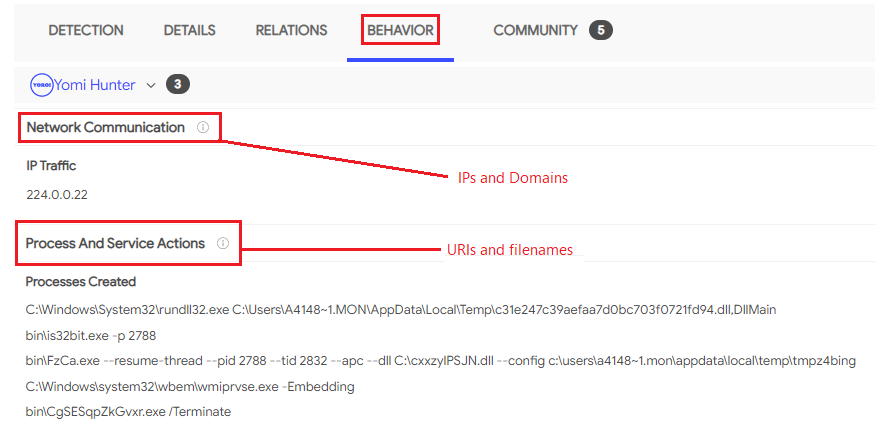
When looking at a new file for the first time, an analyst should establish the basic facts - such as detection rating, file type, size, and if it matches any threat hunting rules. These can then be built upon for the next stages of an investigation.
The next steps include investigating other file attributes that reveal more information about the file, including when it was compiled, when it was first submitted to VT, the filename, the code signing certificate, and other informative attributes.
This information can then be used to tell us more about the file: what type of malware it is and who the adversary who created is.
Good vs Evil 🦸♂️
Silent cartographer 🌎
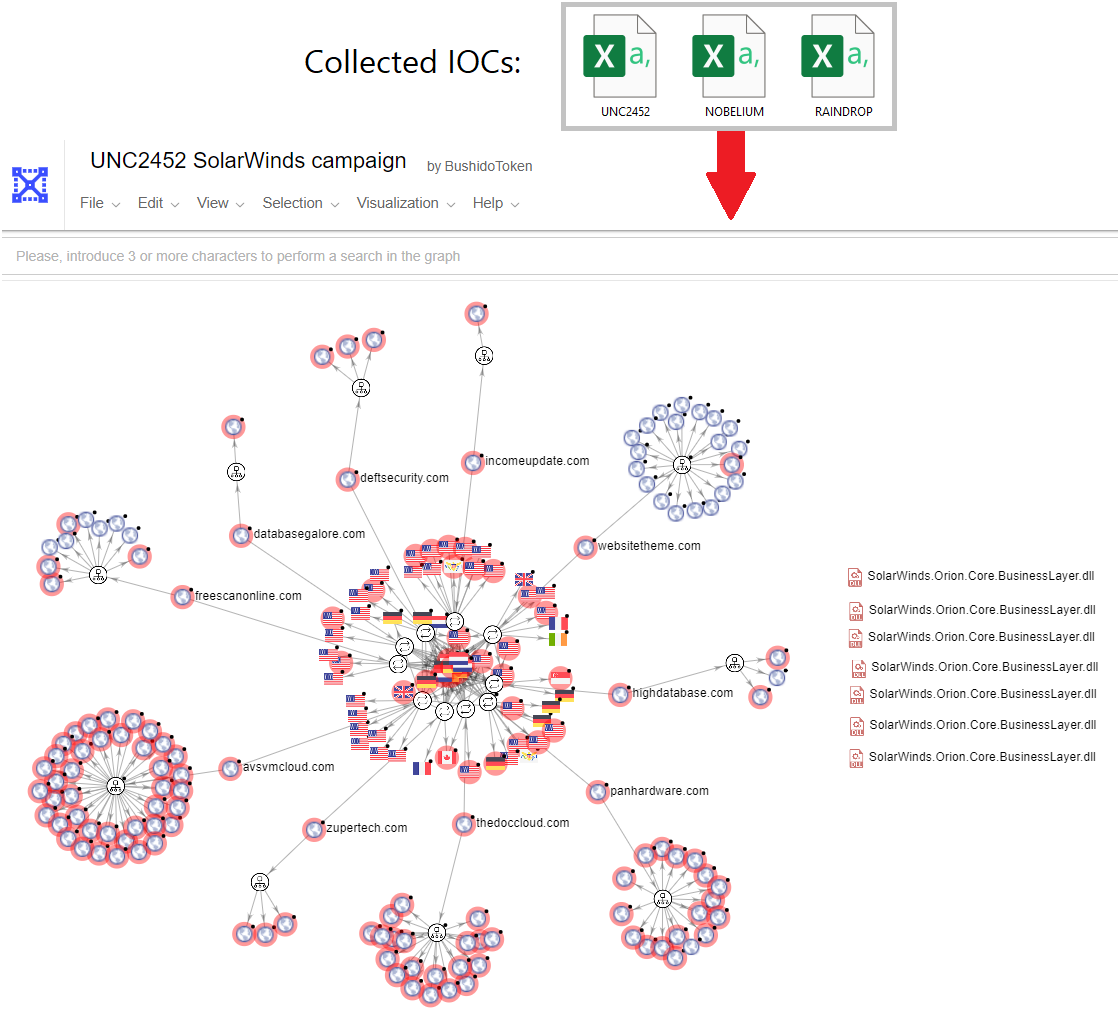
One of Virus Total's most power features is its VT Graph tool. The contents of CSV files can be imported into one graph automatically. VT Graph then maps the relations ships between imported domains, URLs, hashes, and IP addresses and displays them in a presentable format. A researcher can then investigate each IOC more closely and potentially uncover additional campaign artefacts just by double-clicking on each node.
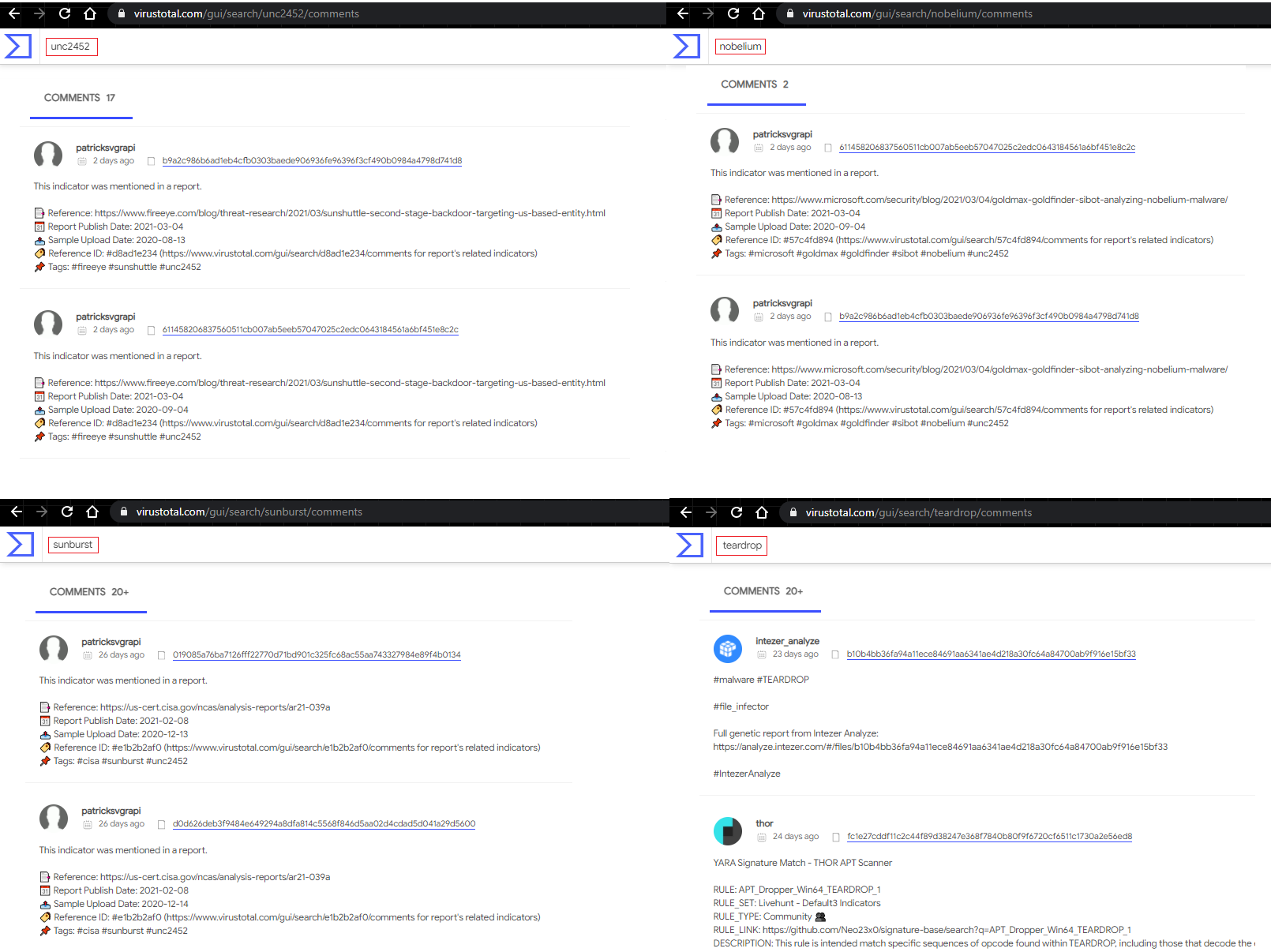
Thrill of the hunt 🕵️♂️
Conclusion
- https://www.virustotal.com/gui/file/0f5d7e6dfdd62c83eb096ba193b5ae394001bac036745495674156ead6557589/detection
- https://www.virustotal.com/graph/embed/g92cdcc51532e43158cb3df4a616ed5b9aedadbada6cb4169811a7174426473d3
- https://www.virustotal.com/gui/search/unc2452/comments
- https://www.virustotal.com/gui/search/sunburst/comments
- https://www.virustotal.com/gui/search/nobelium/comments
- https://www.virustotal.com/gui/search/teardrop/comments
- https://twitter.com/VK_Intel/status/1367176969369096193?s=20
- https://www.virustotal.com/gui/user/BushidoToken/comments
- https://github.com/BushidoUK/Exploring-APT-campaigns